How to Avoid Perimeter Sensor False Alarms: The Definitive Guide
In the architecture of modern security, the perimeter represents the most volatile layer of the defense-in-depth model. Unlike the controlled environment of an interior hallway, the outer boundary of a property is a chaotic theater where hardware must differentiate between a sophisticated breach and the benign movements of the natural world. This tension between sensitivity and reliability creates a fundamental challenge: the false alarm. How to Avoid Perimeter Sensor False Alarms. A system that triggers too frequently ceases to be a security asset and instead becomes a source of “alarm fatigue,” eventually leading users to ignore or disable the very sensors designed to protect them.
Achieving a high-fidelity perimeter requires a move away from the “binary” mindset of simple tripwires. It demands a systemic understanding of how environmental variables—wind, thermal gradients, local fauna, and electromagnetic interference—interact with specific sensing modalities. The financial and psychological costs of persistent false triggers are substantial, ranging from municipal fines for police dispatch to the erosion of trust in the system’s efficacy. Consequently, the goal of perimeter design is not just detection, but the intelligent filtration of noise.
This investigation explores the multi-layered strategies required to harden a perimeter against erroneous triggers. We will examine the physics of different sensor types, the logic of multi-sensor verification, and the governance structures necessary to maintain a silent but vigilant boundary. By treating the perimeter as a dynamic ecosystem rather than a static line, property managers can build a defense that is both hypersensitive to intrusion and resilient to environmental chaos.
Understanding “how to avoid perimeter sensor false alarms”
The challenge of how to avoid perimeter sensor false alarms is rooted in the “Probability of Detection” (Pd) versus the “Nuisance Alarm Rate” (NAR). In a perfect world, these two metrics would be independent, but in physical security, they are inextricably linked. Increasing the sensitivity to catch a slow-moving, low-profile intruder inevitably increases the likelihood that a wind-blown branch or a heavy rainstorm will be interpreted as a threat. Mastering the perimeter involves finding the “sweet spot” on the ROC (Receiver Operating Characteristic) curve where the system is optimized for a specific site’s unique environmental “noise.”
One common misunderstanding is that “smarter” technology, such as AI-driven video analytics, is a panacea for false alarms. While these systems offer significant improvements in object classification, they introduce new failure modes, such as “pixel noise” from insects on the lens or “shadow triggers” during high-contrast solar events. An overreliance on software often leads to neglecting the physical environment—the “low-hanging fruit” of alarm reduction, such as proper vegetation management or the stabilization of fence lines.
Furthermore, we must distinguish between “false alarms” (system malfunctions) and “nuisance alarms” (accurate triggers caused by non-threatening sources like wildlife). Most practitioners group these together, but the solutions differ. A false alarm might require a hardware repair or electrical shielding, whereas a nuisance alarm requires logical filtering or a change in sensing modality. Addressing the root cause requires a forensic approach to data logs rather than a generic adjustment of sensitivity dials.
The Evolution of Perimeter Discrimination
Perimeter security began with mechanical vibration sensors and simple taut-wire systems. These were remarkably effective at detecting someone climbing a fence, but they lacked any ability to filter out the vibrations caused by a passing truck or a gust of wind. The 1980s saw the rise of Passive Infrared (PIR) and Microwave sensors. While these added a layer of sophistication, they were often deployed in “single-tech” configurations, leading to high failure rates in varied weather conditions.
The 1990s and early 2000s introduced “dual-technology” sensors, which combined PIR and Microwave in a single housing. This was a watershed moment: both sensors had to be triggered simultaneously to generate an alarm. This significantly reduced false triggers caused by thermal shifts (which affect PIR) or swaying vegetation (which can affect Microwave).
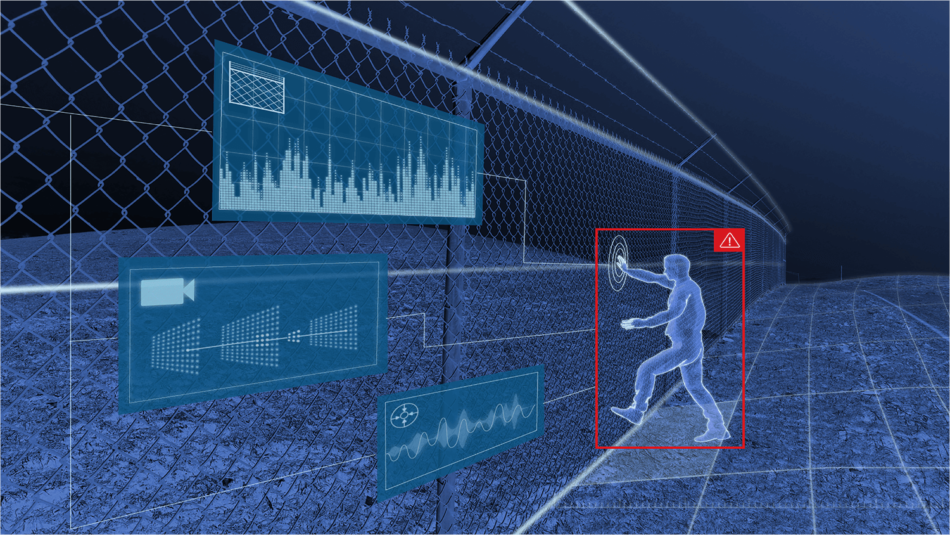
Today, we have entered the era of multi-modal fusion. Modern systems integrate seismic sensors, fiber-optic fence lines, and thermal analytics into a unified logic engine. This “weighted voting” system allows a security controller to ignore a vibration on the fence if the seismic sensors don’t detect footsteps and the thermal camera doesn’t see a human-sized heat signature. The evolution has been a journey from “did something happen?” to “what exactly is happening?”
Conceptual Frameworks: Signal-to-Noise Management
To architect a reliable perimeter, one must apply specific mental models that govern how information is distilled from a chaotic environment.
The “AND” Logic vs. “OR” Logic Framework
In an “OR” configuration, any single sensor can trigger an alarm. This is high-security but high-nuisance. In an “AND” configuration (also known as “Double-Knock”), two or more independent sensors must trigger within a specific time window. Applying “AND” logic is the most effective way to eliminate triggers from isolated environmental events, though it requires careful calibration to ensure it doesn’t create a “blindness” to rapid intrusions.
The Environmental Masking Model
This model suggests that every environment has a “noise floor”—a baseline level of activity. A coastal property has a noise floor dominated by wind and salt-spray interference, while an urban site has a floor dominated by EMI and vibration. Mitigation begins by identifying the dominant frequency of this noise and selecting sensors that operate on a different physical principle.
The Spatial Diversity Framework
This framework posits that sensors should be placed at different heights and angles. If a system relies solely on sensors at ground level, it is vulnerable to small animals. By layering sensors (e.g., a ground-based beam and a fence-mounted vibration sensor), the system can distinguish between a squirrel at 6 inches and a human at 6 feet.
Taxonomy of Perimeter Sensors and Mitigation Trade-offs
Selecting the right sensing modality is the foundational step in reducing inaccuracies. There is no “perfect” sensor; there is only the sensor best suited for the local geography.
| Sensor Technology | Principle of Operation | Primary False Alarm Trigger | Mitigation Strategy |
| Active IR Beam | Light interruption | Fog, birds, falling leaves | Use multi-beam stacks; sync pulses |
| Passive IR (PIR) | Heat differential | Sunlight, small animals | Dual-element sensors; pet immunity lenses |
| Microwave | Doppler shift | Metal movement, heavy rain | Sensitivity gating; dual-tech (PIR/MW) |
| Fence Vibration | Piezo/Accelerometer | Wind, thunder, heavy traffic | Intelligent frequency filtering |
| Seismic | Ground vibration | Nearby trains, roots, pumps | Logic-based “footstep” discrimination |
| Fiber Optic | Light phase shift | Severe storms, falling debris | Zoning; localized sensitivity calibration |
Realistic Decision Logic
If a property is located near a busy highway, a fence-mounted vibration sensor is likely to fail due to constant ambient tremors. In this case, a buried seismic system or a thermal camera with “Human Only” analytics would be a superior choice. The decision logic must prioritize the “environmental immunity” of the sensor over its detection range.
Detailed Real-World Scenarios and Constraints How to Avoid Perimeter Sensor False Alarms
Scenario 1: The Wooded Residential Estate
-
Challenge: High density of deer and low-hanging branches.
-
Failure Mode: PIR sensors triggering every time a deer passes or a branch moves in the wind.
-
The Solution: Implement “cross-zoning” with Active IR beams set to a high “break time” (requiring the beam to be broken for 500ms rather than 50ms). This allows birds and leaves to pass through without an alarm.
Scenario 2: The Coastal Industrial Facility
-
Challenge: High winds and corrosive salt air affecting mechanical sensors.
-
Failure Mode: Galvanic corrosion causing electrical shorts that look like alarms; wind causing “micro-rattles” in fence sensors.
-
The Solution: Use non-mechanical sensors, such as buried fiber optics or thermal analytics, which are housed in NEMA 4X enclosures to prevent environmental degradation.
Scenario 3: The Urban Construction Site
-
Challenge: Significant electromagnetic interference (EMI) and wandering pedestrians.
-
Failure Mode: Microwave sensors “seeing” through thin plywood fences and triggering on people walking on the public sidewalk.
-
The Solution: Shield the back of the microwave sensors and utilize PIR sensors with a narrow “curtain” lens to strictly define the detection boundary within the property line.
Financial Dynamics: The Cost of Inaccuracy
The economics of perimeter security are often hidden. A cheap system with a high false alarm rate is significantly more expensive over a five-year period than a premium, calibrated system.
| Expense Category | Low-Cost / Single-Tech | Professional / Multi-Modal |
| Hardware CapEx | $2,000 | $8,000 |
| Installation/Tuning | $500 | $3,000 |
| False Alarm Fines | $150 per incident | $0 (assuming <1/year) |
| Labor (Guard Response) | $50 – $100 per event | Minimal |
| Security Trust (Loss) | High – System often disabled | High – System remains active |
The “opportunity cost” of a false alarm is the most dangerous variable. If a guard is responding to a false trigger on the North fence, the South fence is momentarily unmonitored—a tactic often used by sophisticated intruders to “test” a system’s response.
Tools, Strategies, and Support Systems
-
Video Verification (The “Human-in-the-Loop”): The single most effective tool for managing false alarms is a camera that automatically slews to the sensor’s location. If the sensor fires, the operator sees why.
-
Sensitivity Schedulers: Using software to automatically lower sensitivity during high-wind events or during hours of high wildlife activity.
-
EMI Shielding: Using ferrites and shielded cabling for all sensor runs to prevent radio frequency interference from acting as a “phantom” trigger.
-
Vegetation Clear-Zones: A physical strategy of maintaining a 3-to-5-foot “sterile zone” around all sensors to prevent botanical interference.
-
Differential Logic Engines: Modern controllers that compare the signals from multiple zones. If 10 zones fire at once, it’s likely a lightning strike or an earthquake, not 10 intruders. The system can auto-discard these as “environmental events.”
-
Periodic Self-Testing: Sensors that “ping” their own receivers to ensure alignment and voltage stability, preventing alarms caused by a slow hardware death.
Risk Landscape: Failure Modes and Compounding Risks
Understanding how to avoid perimeter sensor false alarms requires a taxonomy of what can go wrong when the system is supposedly “working.”
-
The “Blind Spot” Risk: In the attempt to reduce false alarms, managers often over-calibrate or “numb” the sensors. This creates a “Failure to Detect” (FtD) risk, where a slow-moving intruder is ignored by the logic engine.
-
Sensor Drift: Over time, the mounting brackets for IR beams can shift due to soil expansion or thermal cycles. A beam that was centered in June may be on the “edge” of its receiver in December, making it hyper-vulnerable to fog or rain.
-
Power Instability: Low voltage at the end of a long wire run can cause sensors to behave erratically. A 12V sensor receiving 10.5V might trigger randomly as its internal processor struggles with a brown-out state.
Governance, Maintenance, and Seasonal Adaptation
A perimeter is a living entity. It changes as trees grow, as fences sag, and as the seasons shift. Effective governance requires a proactive rather than reactive posture.
The Seasonal Audit Cycle
-
Spring: Clear all new growth. Check for bird nests inside sensor housings. Recalibrate for higher humidity.
-
Summer: Check for “thermal blooming” on PIR sensors as ground temperatures rise. Ensure cooling fans in outdoor enclosures are functional.
-
Autumn: Remove fallen leaves from beam paths. Check for pest ingress (rodents chewing on cables).
-
Winter: Adjust for snow accumulation (which can block low-level beams). Test battery heaters.
Long-Term Adaptation Triggers
If the land adjacent to the property is developed, the noise floor will change. New neighbors may introduce pets, vehicles, or lighting that necessitates a complete re-tuning of the perimeter logic.
Measurement, Tracking, and Evaluation
A robust system is data-driven. Every trigger—whether valid or invalid—must be logged and categorized.
-
The NAR (Nuisance Alarm Rate) Log: A spreadsheet tracking the time, weather conditions, and cause of every alarm.
-
Heat Mapping: Visualizing which zones trigger most often. A “hot” zone usually indicates a physical problem (e.g., a loose fence panel) rather than a sensor problem.
-
The “Success Ratio”: Calculating the percentage of verified detections versus total triggers. A healthy system should maintain a ratio above 95% in controlled environments.
Common Misconceptions and Oversimplifications
-
Myth: “If the sensor is expensive, it won’t have false alarms.”
-
Correction: A $5,000 sensor installed incorrectly is less reliable than a $200 sensor installed with proper environmental consideration.
-
-
Myth: “Sensitivity should always be at 100% to be safe.”
-
Correction: Max sensitivity is almost always a mistake. It captures the “entropy” of the environment rather than the signature of an intruder.
-
-
Myth: “AI can solve all false alarm problems.”
-
Correction: AI is a layer of verification, not a primary detection tool. It still requires clear optics and proper lighting to function.
-
-
Myth: “Buried sensors are foolproof.”
-
Correction: Buried sensors can be triggered by tree roots, underground water pipes, and even heavy rain saturating the soil.
-
Conclusion
The pursuit of a silent perimeter is not a destination but a continuous process of refinement. To truly master how to avoid perimeter sensor false alarms, one must embrace a philosophy of “layered logic.” It is not enough to have the most advanced hardware; one must have the editorial judgment to filter out the irrelevant data that the environment provides.
By combining physical maintenance, multi-modal sensor fusion, and a rigorous data-tracking governance model, property managers can transform their perimeter from a source of frustration into a reliable, high-fidelity security asset. The goal is a system that speaks only when it has something important to say—ensuring that when the alarm finally sounds, it is met with immediate, decisive action rather than doubt.