The Definitive Guide to Wireless Gate Alarm Plans for Property
Securing the perimeter of a property involves more than mere physical barriers; it requires a sophisticated integration of detection, communication, and response protocols. As residential and commercial estates expand in complexity, the traditional “closed-door” policy has evolved into a dynamic monitoring challenge. The gate, wireless gate alarm plans, often hundreds or thousands of feet from the primary structure, represents the first point of vulnerability and the most critical data point in a security perimeter.
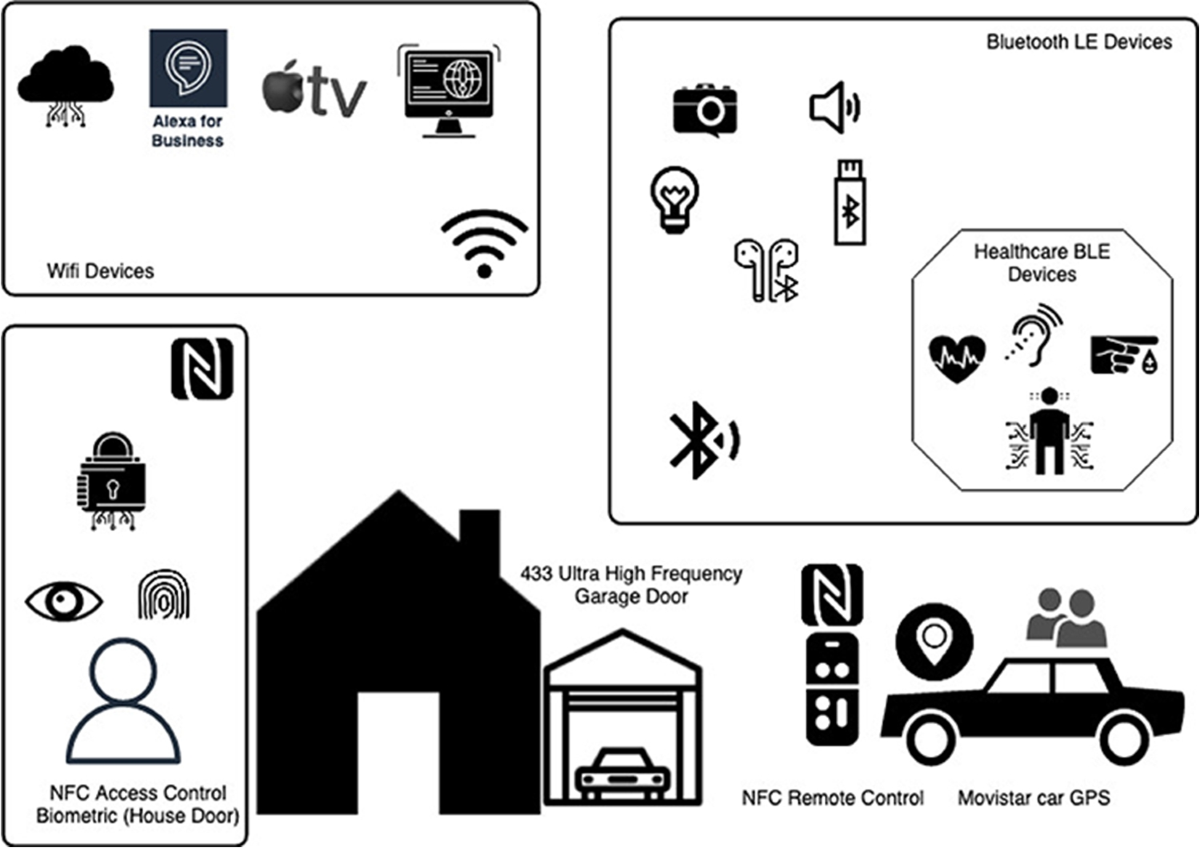
The shift toward wireless technology has fundamentally altered the landscape of property management. Where once the installation of a reliable gate alert necessitated extensive trenching, conduit laying, and high labor costs, modern systems leverage a spectrum of radio frequencies and cellular protocols to bridge the gap. However, this convenience introduces a new set of variables—signal interference, power management, and environmental degradation—that require rigorous planning to mitigate.
This exploration delves into the architectural and strategic nuances of designing a comprehensive security perimeter. It moves beyond the hardware-store “plug and play” mentality, instead focusing on the systemic integration of sensors, receivers, and logic-based responses. By analyzing the structural requirements of these systems, we can better understand how to build a defense-in-depth strategy that remains resilient over years of exposure to the elements and shifting technological standards.
Understanding “wireless gate alarm plans.”
At its core, a wireless gate alarm plan is a blueprint for extending a property’s “nervous system” to its furthest physical limits. It is a common misunderstanding to view these plans as mere shopping lists for hardware. In reality, a plan must account for the topographical, electromagnetic, and behavioral realities of a specific site. An oversimplified approach often fails because it ignores the inverse square law of signal propagation or the impact of seasonal foliage on 433 MHz or 900 MHz frequencies.
A robust plan distinguishes between “annunciation” and “alarm.” Annunciation is the simple notification that a gate has been opened—useful for a delivery truck but insufficient for a security breach. An alarm implies a structured response, perhaps involving logged data, photographic capture, or secondary sensor verification. When developing wireless gate alarm plans, one must weigh the trade-offs between high-frequency bandwidth (which allows for video) and low-frequency penetration (which ensures a basic “open/closed” signal reaches the house through a dense treeline).
Furthermore, the “wireless” aspect is rarely absolute. Every wireless node requires a power strategy, typically involving solar arrays or high-capacity lithium-thionyl chloride batteries. Neglecting the power-draw cycle in the planning stage results in a system that is functionally useless during consecutive days of overcast weather or during the high-drain cycles of winter. True mastery of this domain involves balancing these invisible physical constraints against the desired user outcome.
The Evolution of Perimeter Monitoring
The lineage of the modern gate alarm begins with mechanical tripwires and pressure plates, systems that were reliable but lacked the ability to distinguish between a trespasser and a stray animal. As electronics matured in the mid-20th century, hardwired magnetic reed switches became the gold standard. While effective, the prohibitive cost of burying wire over long distances limited these systems to high-value industrial sites or the extremely wealthy.
The introduction of the 433 MHz and 315 MHz ISM (Industrial, Scientific, and Medical) bands democratized perimeter security. These frequencies allowed for low-power, long-range transmission that could bypass most architectural obstacles. However, early wireless systems were plagued by “collision” issues—multiple sensors firing at once and canceling each other out—and lacked encryption, making them susceptible to “replay attacks” where a signal could be captured and retransmitted by an intruder.
Today, we have entered the era of spread-spectrum technology and mesh networking. Modern systems often utilize LoRa (Long Range) or proprietary encrypted sub-GHz frequencies that can travel miles while consuming milliwatts of power. The evolution has moved from simple detection to intelligent discrimination, where the system can identify the specific signature of a vehicle versus a pedestrian, adjusting the alert level accordingly.
Conceptual Frameworks and Mental Models
To design a resilient system, one must apply specific mental models that govern how information travels across a physical space.
The Fresnel Zone Model
This framework considers the elliptical space between the transmitter and the receiver. It isn’t enough to have a “line of sight” in a narrow sense; if the ground or a nearby wall encroaches on the Fresnel zone, the signal will reflect and cause phase cancellation. Planning for a gate alarm requires elevating antennas to keep this zone clear, ensuring the signal remains “coherent.”
The “False Positive” vs. “Dead Zone” Trade-off
Every security plan exists on a spectrum. A system tuned for high sensitivity will catch every intruder but will also trigger for a deer or a heavy rainstorm, leading to “alarm fatigue” where the user eventually ignores the alerts. Conversely, a desensitized system avoids false positives but risks a dead zone where a slow-moving or shielded intruder goes unnoticed.
The Energy Budget Framework
Wireless systems are governed by the laws of thermodynamics. A sensor’s “duty cycle”—how often it checks for a breach and how often it “pings” the base station—dictates its lifespan. A plan must calculate the milliamp-hours required for the radio’s highest-power state (transmission) versus its “sleep” state, adjusted for local temperature extremes,s which can sap battery capacity by up to 40%.
Taxonomy of Sensor Technologies
Selecting the right sensing modality is the most critical decision in any wireless gate alarm plan. Each technology possesses inherent strengths and catastrophic weaknesses depending on the environment.
| Technology | Primary Use Case | Advantage | Disadvantage |
| Magnetic Reed | Swing/Slide Gates | Extremely low power | Requires precise alignment |
| PIR (Infrared) | Driveway approach | Detects heat signatures | High false triggers from the sun/wind |
| Magnetometer | Vehicle detection | Invisible (buried) | Only detects moving metal |
| Active IR Beam | Narrow gaps/fences | Precise “invisible fence.” | Fog/heavy rain can break the beam |
| Microwave | High-security zones | Penetrates obstacles | Can “see” through thin walls, causing false alarms |
| Photoelectric | General perimeter | Long range | Vulnerable to bird/leaf interference |
Decision Logic for Category Selection
If the goal is to monitor a remote farm gate where cattle are present, a magnetometer buried in the ground is superior to a PIR sensor, as the cattle won’t trigger the metallic detection. However, if the goal is to prevent human scaling of a pedestrian gate, an active IR beam paired with a reed switch provides the necessary dual-verification to ensure the gate is both physically closed and not being bypassed.
Detailed Real-World Implementation Scenarios for wireless gate alarm plans
Scenario 1: The High-Acreage Rural Estate
-
Constraint: The gate is 2,500 feet from the house, separated by a dense oak grove and a topographical rise.
-
The Plan: Utilize a 900 MHz LoRa-based system. High-frequency 2.4 GHz (Wi-Fi) would fail here due to foliage absorption.
-
Failure Mode: Seasonal changes. A signal that works in winter may fail in summer when moisture-heavy leaves act as a giant RF sponge.
-
Second-Order Effect: The need for a solar-charged repeater station at the crest of the hill to maintain signal “velocity.”
Scenario 2: The Urban Commercial Yard
-
Constraint: High electromagnetic interference (EMI) from nearby power lines and competing Wi-Fi networks.
-
The Plan: Frequency-hopping spread spectrum (FHSS) sensors. These cycle through multiple frequencies to find a clear path.
-
Decision Point: Hardening the receiver against “jamming” or signal flooding, which is a common tactic for sophisticated theft in urban centers.
Scenario 3: The Coastal Residential Property
-
Constraint: Salt air corrosion and high-velocity winds.
-
The Plan: NEMA 4X-rated enclosures with non-metallic components to prevent galvanic corrosion. Magnetic switches must be hermetically sealed in glass or high-grade plastic.
-
Failure Mode: “Wind-trip” where the gate vibrates enough to momentarily separate the magnet from the sensor, triggering a false alarm. The plan must include a “debounce” delay in the logic.
Planning, Cost, and Resource Dynamics
The true cost of a wireless gate alarm is rarely the purchase price; it is the “cost of ownership” over a five-year horizon. This includes battery replacement cycles, hardware degradation, and the potential opportunity cost of a failed system.
| Resource Category | Entry-Level (DIY) | Professional/Industrial | Custom Integrated |
| Initial Hardware | $150 – $400 | $1,000 – $3,500 | $5,000+ |
| Installation Labor | $0 (Self) | $500 – $1,500 | $2,000+ |
| Annual Maintenance | $50 (Batteries) | $150 (Pro-service) | $500+ (Managed) |
| Signal Range | 100 – 400 ft | 1,000 – 5,000 ft | Multi-mile/Satellite |
Direct costs are easily tabulated, but indirect costs—such as the time spent troubleshooting “phantom” alerts or the potential insurance premium hike after a missed breach—must be factored into any serious wireless gate alarm plans. High-quality components often pay for themselves within 24 months through reduced maintenance calls alone.
Risk Landscape and Failure Analysis
A security system is only as strong as its most neglected variable. In the context of wireless gate alarms, failure is rarely a complete system blackout; it is more often a subtle degradation.
Taxonomy of Risks
-
RF Shielding: A large vehicle parked directly in the line of sight between the transmitter and receiver can effectively “blind” the system.
-
Environmental Masking: Heavy snow accumulation on a solar panel prevents charging, leading to a slow death of the sensor over 72 hours.
-
Signal Collision: In dense residential areas, a neighbor’s identical system on the same frequency can cause “packet loss,” where your receiver misses a trigger because it was “listening” to the neighbor’s data.
-
Biological Interference: Spiders spinning webs over IR lenses or wasps nesting in the antenna housing can attenuate signals or cause constant false triggers.
Compounding Risks
The most dangerous scenario is the “correlated failure.” For example, a severe storm may cause a power outage at the main house (disabling the receiver) while simultaneously causing wind-blown debris to trigger the gate sensor. Without a battery-backed receiver, the event is never logged, and the security lapse goes unnoticed until morning.
Governance, Maintenance, and Long-Term Adaptation
A “set and forget” mentality is the primary cause of system failure. Effective management requires a layered checklist approach to ensure the system evolves with its environment.
The Maintenance Lifecycle
-
Quarterly: Clean all lenses and housings. Check for insect ingress. Test battery voltages under load.
-
Semi-Annually: Perform a “signal walk-test.” Verify that the signal strength (RSSI) hasn’t dropped due to new construction or vegetation growth.
-
Annually: Review logs for “pattern failures.” Are there specific times of day when false alarms peak? This may indicate sun glare affecting a PIR sensor or local radio interference.
Adjustment Triggers
If the property undergoes landscaping, the “wireless gate alarm plans” must be updated. A new stone pillar may look aesthetically pleasing, but can act as an RF shield, requiring a relocation of the transmitter or the use of an external high-gain antenna.
Measurement, Tracking, and Evaluation
How do you measure the success of a system that is designed to do nothing most of the time? We look at leading and lagging indicators.
-
Leading Indicators: Battery health telemetry, signal-to-noise ratio (SNR) trends, and successful daily “heartbeat” pings from the sensor to the hub.
-
Lagging Indicators: Number of missed entries (detected via secondary means like cameras), mean time between false alarms (MTBFA), and response time from alert to human intervention.
Documentation Examples
-
The Signal Map: A plot of the property showing decibel (dBm) readings at various points. This serves as a baseline for future troubleshooting.
-
The Event Log: A structured record of every “open/close” cycle, which can reveal unauthorized usage patterns that don’t necessarily trigger an “alarm” state.
Common Misconceptions and Oversimplifications
-
Myth: “Long-range” means it will work through anything.
-
Correction: Range ratings are calculated in “open field” conditions. A 1-mile rated system may struggle at 500 feet if forced to penetrate concrete walls or dense wet timber.
-
-
Myth: Wi-Fi is the best choice because it connects to my phone.
-
Correction: Wi-Fi is power-hungry and has poor range. Sub-GHz frequencies are far more reliable for perimeter work, using a bridge to connect to the internet only at the base station.
-
-
Myth: Solar power is “maintenance-free.”
-
Correction: Solar panels require cleaning and battery replacement every 3–5 years. They are also vulnerable to hail and UV-induced clouding.
-
-
Myth: Encryption isn’t necessary for a gate alarm.
-
Correction: Without encryption, a simple “code grabber” can mimic your gate’s signal, allowing an intruder to suppress the alarm before entering.
-
Synthesis and Adaptability
The creation of wireless gate alarm plans is a study in managing the tension between physical security and electronic reliability. A definitive system is never a static installation; it is a living architecture that must be tuned to the specific “noise” of its environment. Whether protecting a suburban driveway or a sprawling industrial yard, the principles remain the same: prioritize signal integrity, account for environmental degradation, and build in redundancy.
The most successful implementations are those that acknowledge the limits of technology. By combining different sensing modalities—such as a magnetic reed switch for the gate itself and a buried magnetometer for the driveway—the property owner creates a “logic gate” that filters out the chaos of nature and highlights only the true threats. In the end, the goal of a gate alarm is not just to make noise, but to provide the clarity and time necessary for an informed response.






