Warehouse Perimeter Surveillance Risk Control: The 2026 Strategic Guide
In the high-stakes environment of global logistics, the warehouse perimeter has evolved from a simple property boundary into a sophisticated front line of risk mitigation. Modern warehouse perimeter surveillance risk control is no longer a peripheral concern handled by a padlock and a nightly patrol; it is a complex, integrated discipline that sits at the intersection of civil engineering, digital intelligence, and behavioral psychology. As supply chains face increasing pressure from both organized criminal syndicates and the volatility of localized social disruptions, the ability to maintain a resilient exterior has become a primary driver of operational continuity and insurance viability.
The challenge of securing a warehouse exterior is rooted in its inherent exposure. Unlike the interior of a facility, which benefits from climate control and structural shielding, the outdoor perimeter is subject to the entropy of the natural world—weather-driven sensor degradation, shifting topography, and the unpredictable movements of third-party logistics partners. Effectively managing these risks requires an analytical framework that prioritizes “detection depth” over mere physical height. A fence, regardless of its construction, is only as effective as the surveillance logic that monitors it.
In 2026, the industrialization of theft has reached a level of technical parity with security systems. Intruders now employ a range of adversarial tactics, from signal-jamming of wireless mesh networks to the use of thermal-masked reconnaissance drones. Consequently, the strategic objective has shifted from “denial of entry” to the “compression of response time.” This article explores the architectural and technical methodologies required to build an adaptive, intelligence-led perimeter that can withstand both the overt and the subtle risks of the modern era.
Understanding “warehouse perimeter surveillance risk control”
To engage with warehouse perimeter surveillance risk control is to recognize that “surveillance” is not merely the act of watching; it is the act of verifying intent. A common misunderstanding in facility management is the conflation of coverage with control. A facility may have 100% camera coverage of its fence line and yet possess zero risk control if those cameras are unmonitored or if their alerts are lost in a sea of false positives generated by swaying branches or passing wildlife.
The discipline requires a multi-perspective assessment that balances the “Hard” (physical barriers), the “Soft” (digital sensors and analytics), and the “Human” (response protocols). From a risk perspective, the perimeter is a data source. Every sensor, whether it is a fiber-optic vibration cable or a long-range radar, is a node in a logic chain designed to answer one question: Is this movement a threat? Oversimplification occurs when managers view security as a product—a one-time purchase of hardware—rather than a living system that requires constant calibration against the shifting tactics of adversaries.
True risk control is achieved through “Alert Fidelity.” This involves filtering the noise of the outdoor environment so that when a security professional is notified of a breach, there is a 95% or higher probability that a genuine intrusion is occurring. Without this fidelity, the system defaults to a state of “Alert Fatigue,” where the human response—the most critical part of the security chain—is neutralized by skepticism and delay.
The Systemic Evolution of Logistics Security
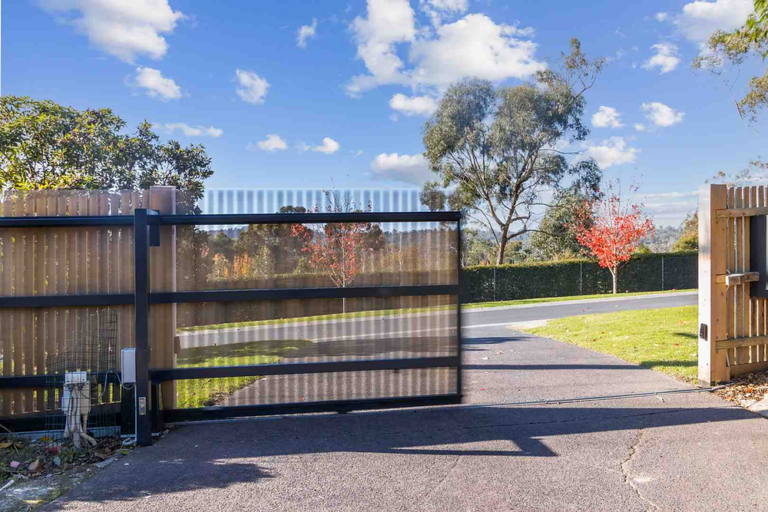
The history of the warehouse perimeter is a transition from “Fortification” to “Cognition.” In the mid-20th century, risk management was a function of physical mass—concrete walls, heavy gates, and the presence of armed guards. The logic was simple: make the effort of entry exceed the reward of theft. However, as warehouses grew into multi-million-square-foot fulfillment centers, the “Castle” model became economically and operationally unfeasible.
The 1990s introduced the “Electronic Perimeter,” utilizing the first generation of analog CCTV and microwave sensors. This era moved the needle from denial to detection, but it was plagued by a high “False Alarm Rate” (FAR). The 2010s saw the arrival of the “Networked Perimeter,” where IP-based systems allowed for remote monitoring. Today, in 2026, we have entered the “Predictive Perimeter” era. Modern surveillance now leverages “Edge AI” to identify pre-incident behaviors—such as a vehicle circling the property three times or a person lingering near a weak point in the fence—before a breach ever occurs.
Conceptual Frameworks: The Logic of Exterior Defense
Professional risk managers utilize specific mental models to structure their defensive investments. These frameworks ensure that hardware serves a strategic purpose rather than being a decorative expenditure.
1. The 5-D Framework
This classic model dictates that every perimeter layer must perform five distinct functions:
-
Deter: Psychological barriers (lighting, signage) that discourage the attempt.
-
Detect: Identifying the breach attempt as it begins.
-
Deny: Physical hardening that prevents immediate entry.
-
Delay: Forcing the intruder to spend more time on-site, providing time for a response.
-
Defend: The active human or automated intervention to stop the threat.
The limitation of this model is its linear nature; modern risks often bypass “Deter” and “Deny” via aerial or cyber means.
2. CPTED (Crime Prevention Through Environmental Design)
CPTED focuses on the “Passive” management of risk through site layout. By maintaining “Natural Surveillance” (clear sightlines) and “Territorial Reinforcement” (defining public vs. private space), the property becomes inherently less attractive to criminals. However, CPTED is often defeated by “Shadow Zones”—areas where landscaping or structural additions create blind spots that sensors cannot reach.
3. The Onion Model (Defense in Depth)
This model posits that the perimeter is not a line, but a series of concentric zones. For a warehouse, this starts at the “Approach Zone” (public roads), moves to the “Boundary Zone” (fences), the “Yard Zone” (docking areas), and finally the “Shell Zone” (the building itself). Risk is managed by ensuring that no single failure leads to a total loss.
Strategic Categories and Infrastructure Trade-offs
Warehouse perimeters vary significantly based on their location (urban vs. rural) and the value density of the inventory.
| Category | Primary Surveillance Mechanism | Advantage | Major Trade-off |
| Active Hardened | Electric Fencing + Video Analytics | High physical deterrent | High maintenance; liability risks. |
| Virtual Perimeter | Radar + Long-range PTZ Cameras | Stealth; low physical footprint | High cost; zero physical delay. |
| Hybrid Integrated | Fiber-Optic Sensors + AI Monitoring | Extremely high alert fidelity | Complexity; requires high-end SOC. |
| Acoustic/Tactile | Ground sensors + Audio analytics | Invisible; weather-resistant | Susceptible to heavy vehicle noise. |
| Rapid Deployable | Solar-powered Mobile Towers | Flexibility for new construction | Vulnerable to theft of the unit itself. |
Decision Logic for Risk Profiling
A “High-Velocity” fulfillment center storing consumer electronics requires a Hybrid Integrated approach to manage the risk of rapid, organized cargo theft. Conversely, a bulk material warehouse (lumber or steel) may prioritize Active Hardened physical barriers with minimal electronic surveillance, as the “Asset Portability” is low.
Operational Scenarios and Failure Mode Analysis warehouse perimeter surveillance risk control

Scenario 1: The “Low-and-Slow” Breach
An intruder uses a specialized kit to bypass a magnetic gate lock by introducing a physical shim.
-
Surveillance Failure: The camera was positioned too high to see the minute hand movements at the gate latch.
-
Risk Control Failure: The door contact was bypassed, and no “Heartbeat” alert was sent to the monitoring center.
-
Result: Unauthorized entry without an alarm trigger.
Scenario 2: The Environmental “White-Out”
During a heavy fog or snowstorm, the facility’s standard visible-light cameras become 80% obscured.
-
Constraint: The facility lacked thermal imaging.
-
Failure Mode: Organized thieves use the weather as “Natural Camouflage” to cut through a rear fence section.
-
Response: The system fails to “Detect” because the analytics cannot distinguish between the snow and a human form.
Economic Dynamics: Costs and Resource Allocation
Investing in warehouse perimeter surveillance risk control is an exercise in “Asymmetric Mitigation.” The cost of a system is linear, but the potential loss from a single “Sophisticated Burglary” is exponential.
Annualized Cost-Risk Matrix (Estimated for 500k sq. ft. Facility)
| Investment Area | Direct Cost (Capital) | Annual OpEx | Risk Mitigation Value |
| Physical Hardening | $80k – $250k | $5k (Repair) | High (Denial/Delay) |
| AI Surveillance Network | $120k – $300k | $15k (Licensing) | Highest (Detection) |
| Professional Monitoring | N/A | $30k – $80k | Critical (Response) |
| Systemic Auditing | $10k (Once) | $5k (Recurring) | Essential (Governance) |
The Variability of Scale: The “Cost per Linear Foot” for securing a square perimeter is 25% lower than securing an irregular, L-shaped property due to fewer camera poles and easier signal trenching.
Technical Support Systems and Strategic Tooling
-
LiDAR (Light Detection and Ranging): Unlike cameras, LiDAR creates a 3D point cloud of the perimeter, allowing for precise “Spatial Violation” detection that is immune to shadows and glare.
-
Multi-Spectral Imaging: Combining thermal and visible light allows a system to “see” a human heat signature through dense foliage while still providing identifying visual details for law enforcement.
-
Encrypted Wireless Mesh: For remote sections of the perimeter where trenching is impossible, 256-bit encrypted mesh networks prevent adversaries from “sniffing” or jamming the video feed.
-
Audio Analytics: Microphones that can detect the specific frequency of “Glass Breaking” or “Metal Cutting” provide a secondary, non-visual layer of verification.
-
Autonomous Drone Responders: When a fence sensor is triggered, an automated drone launches to provide a “Top-Down” view of the intruder before security guards arrive.
-
Edge Analytics: Processing the video at the camera ensures that even if the network is cut, the camera can store the “Incident Metadata” and continue to operate its local deterrence (e.g., sirens/strobe lights).
The Risk Landscape: Compounding Vulnerabilities
Risk is rarely a singular event. In a warehouse environment, vulnerabilities tend to compound:
-
Proximity Risk: A warehouse located near a highway on-ramp has a higher risk of “Rapid Extraction” theft.
-
Operational Leakage: When employees use unauthorized perimeter gates for cigarette breaks, they create “Patterns of Opportunity” that are easily identified by external scouts.
-
The “Shadow IT” Risk: Unsecured outdoor IoT devices (like smart lighting or weather sensors) can be used as “Pivot Points” for a cyber-attacker to gain access to the warehouse’s internal inventory management system.
Governance, Maintenance, and Adaptive Oversight
A perimeter surveillance system is a decaying asset. Environmental wear and tear can reduce a system’s effectiveness by 15% annually if not properly governed.
The Lifecycle Governance Checklist
-
Weekly: Remote verification of camera “Field of View” (checking for lens drift or cobwebs).
-
Monthly: Physical inspection of “Tamper Switches” on all exterior enclosures and gate motors.
-
Quarterly: “Red Team” testing—attempting to approach the perimeter undetected to test the sensitivity of the AI analytics.
-
Annually: Landscape audit—ensuring that tree growth has not created “Natural Ladders” or obstructed the path of infrared beams.
Measurement, Tracking, and Evaluation Metrics
Effective risk control is measured through “Leading” and “Lagging” indicators.
-
Leading Indicator: Mean Time to Verification (MTTV). The number of seconds between a sensor trip and a human monitor confirming the cause. A target MTTV in 2026 is under 45 seconds.
-
Lagging Indicator: Shrinkage Rate. The percentage of inventory loss attributed to “External Breach” versus “Internal Theft.”
-
Documentation Example: A “Vulnerability Register” should be maintained, documenting every “Sensor Blind Spot” and the corresponding timeline for its remediation.
Common Misconceptions and Strategic Errors
-
Misconception: “Our perimeter is safe because we have 24/7 guards.”
-
Reality: Human guards are subject to boredom and limited sightlines. A guard is a responder, not a sensor. Surveillance technology must empower the guard, not be replaced by them.
-
-
Misconception: “High-resolution cameras are better for security.”
-
Reality: Resolution is secondary to “Dynamic Range.” A 4K camera that cannot see into a dark shadow next to a bright streetlight is less useful than a 1080p camera with high WDR (Wide Dynamic Range).
-
-
Misconception: “Fences stop criminals.”
-
Reality: Fences are psychological hurdles and physical “delays.” A determined thief with a $100 power tool can breach any fence in under 60 seconds. The surveillance system must detect the approach, not the breach.
-
Conclusion: The Future of Autonomous Resilience
The mastery of warehouse perimeter surveillance risk control is an ongoing pursuit of situational awareness. As we look toward the late 2020s, the “Reactive” model of security is dying. The future belongs to “Autonomous Resilience”—systems that can not only detect an intruder but can also self-diagnose a sensor failure, adjust camera angles in real-time to track a moving target, and integrate with municipal law enforcement data to predict theft trends before they arrive at the gate.
For the facility manager, the goal remains unchanged: to create an environment where the “Cost of Theft” is consistently higher than the “Reward of Theft.” By leveraging a layered, intelligence-led surveillance strategy, the warehouse transforms from a vulnerable storage box into a hardened, self-aware node in the global supply chain. Resilience is not found in the height of the wall, but in the speed of the data that protects it.